One-off pentest
A clear snapshot of your security
A one-off pentest gives you a clear, independent assessment of your current security posture. Ideal for compliance requirements like ISO 27001 or SOC 2, it delivers documented findings, risk prioritization and a professional report you can share with auditors and stakeholders. You gain clarity on your most critical vulnerabilities, quickly and efficiently, with the option to expand into continuous or 24/7 testing as your security needs grow.

In or out of the box
Ways to perform a Pentest
A pentest focuses on how systems behave when they are tested in different ways. Within the defined scope, we look at what can be accessed, changed or combined, and how these actions relate to each other.
Pentests can be conducted in various ways, depending on what is being tested and how much information a tester receives beforehand.
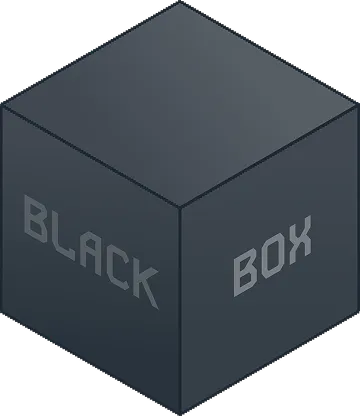
Black Box
No information
The hacker starts completely from the outside, without access to documentation or accounts. This gives a good view of what a random attacker from outside can achieve.
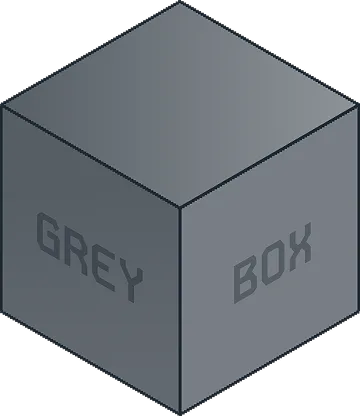
Grey Box
partial information
The hacker receives some information, such as an account or API description. This allows the investigation to delve deeper more quickly and also reveals errors in the functioning of applications.
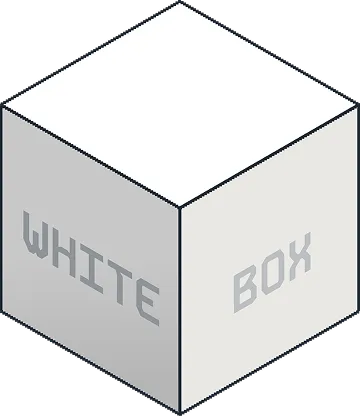
White Box
full information
The hacker has full access to source code, configuration, and architecture. This makes hidden vulnerabilities visible and can prevent many issues early in development.
In or out of the box
Getting
started
with
One-off pentest
Digital intake
White, grey, or black box. For web apps, APIs, or complete platforms. Our community tests what you build — as often as you need.
Define your intensity
Whether you need dedicated pentesting hours each month or continuous scanning at the frequency you choose — the pack adapts to your environment.
Woolves activated
Once you implement a solution, hackers will test again. What is fixed, stays fixed.
Make it safe
New releases are automatically included. This creates an ecosystem where security grows with your product: proactive security instead of reactive control.
Retest
Every finding appears directly in the Woolves platform. Clear, structured, including impact, risk, and reproduction instructions.
Report
Once you implement a solution, hackers will test again. What is fixed, stays fixed.

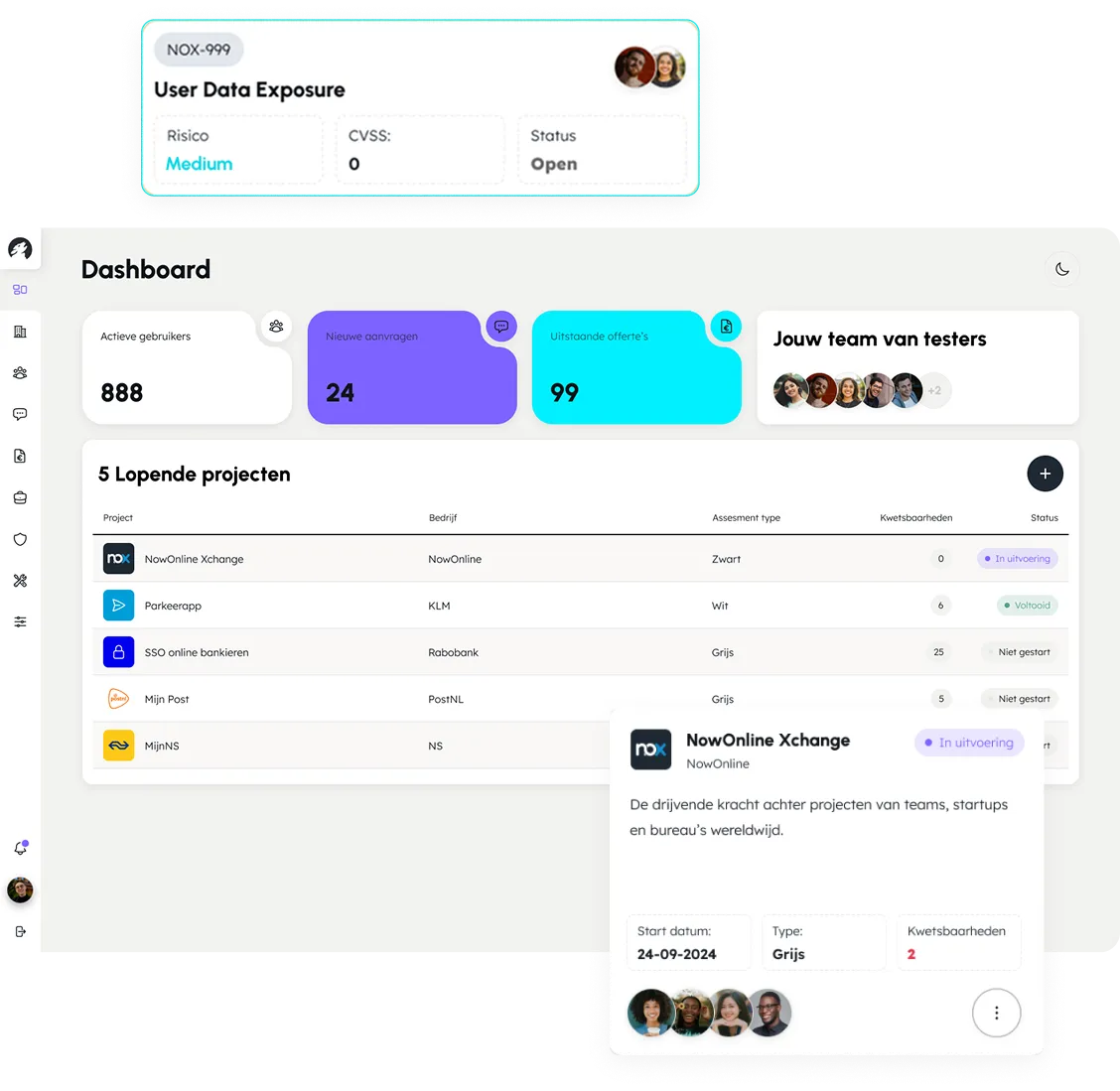
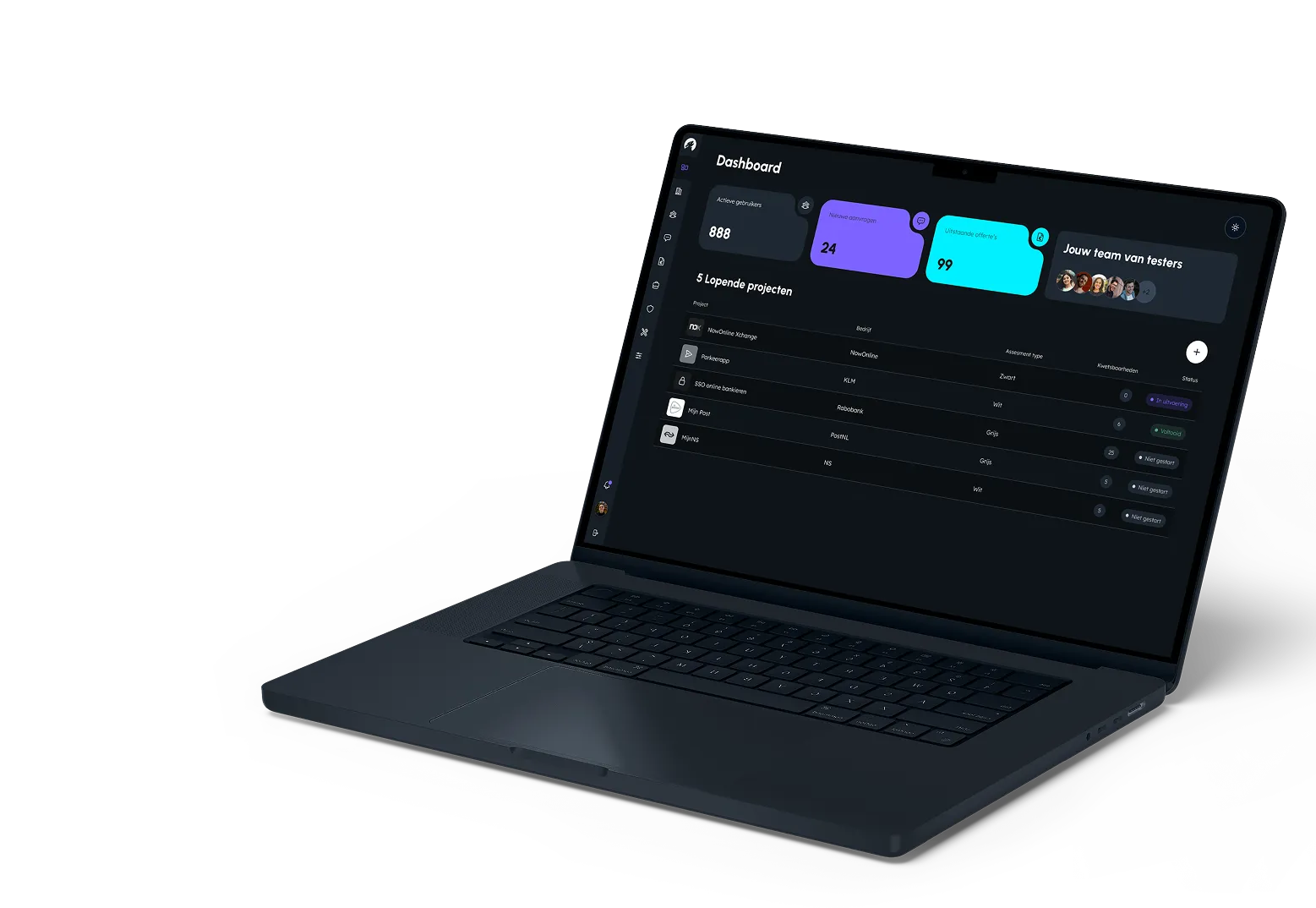
Woolves platform
From insight to action, in one place
The Woolves platform brings testing, reporting, and learning together in one place.
Findings appear instantly in a clear interface that fits your development workflow. Issues, priorities, and fixes sit side by side, so teams move faster and keep knowledge where it belongs.
features & pricing
Security as a habit
Choose a plan that fits your needs,— from an initial check to continuous security.
These organizations have already been hacked by us
Organizations across various sectors work with Woolves to reduce their digital risk.
>_ get started now
Predator precision,
protector mindset
protector mindset
Choose a plan that fits your needs, from an initial check to continuous security.

>_ schedule a demo
Make your software safer and your team stronger
Schedule a demo and see how continuous security becomes a natural part of your development process.